ICS CyberSec– No Reason for Optimism as hackers are having an easy time

ICS CyberSec Conference 2019
The fourth annual ICS Cybersec cyber defense conference focusing on Industrial Control Systems was held in Israel this September and I was fortunate to participate. Since the Israeli market has an inordinately large proportion of industrial solution providers, it was an ideal setting for such an event and a good place to meet with people in the sector.
The conference, which was chaired by Daniel Ehrenreich, featured industry experts who spoke about the latest and most creative technologies in the cybersecurity arena.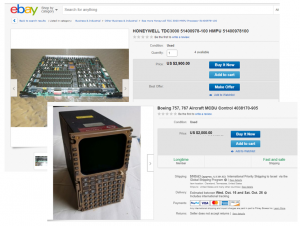
The conference keynote was delivered by Oren Israel, who is the Director of Israel’s ICS Center, part of the National Cyber Directorate. The Directorate heads all aspects of cyber security for civilian entities (non-military) including technology, standards and defence. Daniel Ehrenreich’s thoughtful and unique insights during the event added a lot of value to the other speaker’s points.
The ICS Cybersec keynote address pointed out that the future of cybersecurity was not looking very bright. In fact, in Mr Oren Israel’s words, he said — “There is no reason to be optimistic”. In his talk, he explained how it was now very simple for even lower end hackers to set up home labs with ICS equipment that they could buy cheaply off eBay. They could then use the available list of ICS/OT vulnerabilities and exploits from the web and get started on the hacking game.
It was disheartening to hear that the very tools that were developed to probe and discover weaknesses are now being used by hackers for malicious activities. However, the positive aspect that came through is that the Directorate is about to launch a new set of guidelines and a country-wide ICS Security framework. The new framework has been created to addresses everything from board level strategy and risk management to practical recommendations to have secure ICS/OT environments
The Directorate has also established an ICS Security lab that enables vendors, researchers and end users to test multiple scenarios in a real-world environment. The Directorate has also produced standards for dealing with the supply chain, assessing and certifying supplier with regards to their level of cyber readiness.
Business Continuity – Evolving the Discussion
Business continuity is an organization’s ability to ensure operations and core business functions are not severely impacted by a disaster or unplanned incident that take critical systems offline. This was one of the key topics that several speakers voiced their opinions about. The need to improve the discussion surrounding ICS Cyber security, specifically to focus the discussion on “Business Continuity” is of paramount importance in today’s times.
[optin-monster-shortcode id=”dv4jqlr9fih8giagcylw”]
As we have seen in the aftermath of several high-profile attacks, including the most recent Norsk Hydro incident, the ability of a company to fully recover from an attack, the impact on its production capabilities and longer-term costs have very real consequences on the company’s bottom line. This is apart from the way the company’s top management and board members felt about their current positions.
Companies, in most cases, are in the business of generating a profit for their shareholders. Moving the ICS Cyber discussion further up the food chain makes a lot of sense since talking to company executives and other stakeholders in a language they are familiar with can bring about more change.
The biggest issue for vendors will be proving the business case to companies that see ICS Cyber Security as a necessary evil. Overcoming this will take time but can be achieved by positioning ICS Cyber Security as part of the company’s overall value proposition. Whether customers are buying gas, electricity or pharmaceuticals, they would still like to know that you are prepared for every eventuality.
IT/OT Converging but from Different Directions
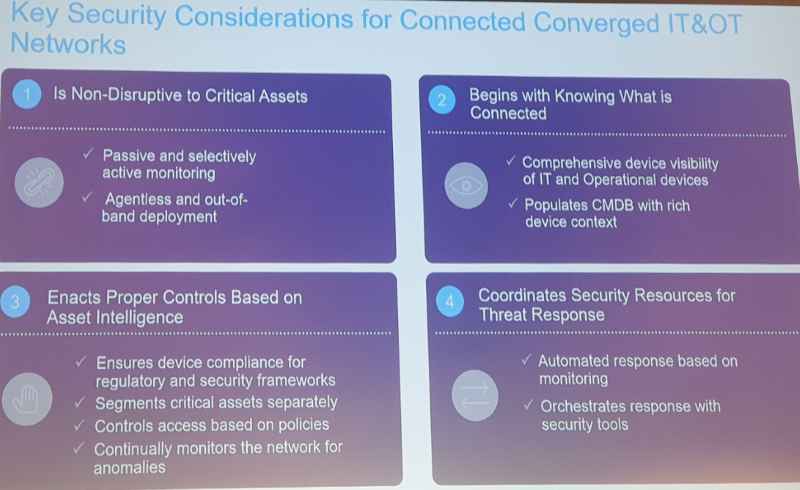
Another recurring theme at ICS Cybersec that speakers broached upon was Convergence. Vendors such as Checkpoint and Forescout showcased their wares with a decidedly different approach to IT/OT convergence.
For example, Checkpoint partners with several ICS/OT Cyber Security specialists (Claroty, Indegy, Armis, Cynerio, Medigate, Cyber MDX and more) mainly to gather ICS/OT/SCADA data and feed it into their own IoT/ICS security solution. During our discussions Checkpoint’s SCADA solutions expert, Shlomi Feldman, pointed out that the vast majority ICS/OT attacks had been initiated through the corporate network and that many threats had inadvertently come into the SCADA networks. While Checkpoint’s approach is to cover all bases, they suggest many of the attacks/threats can be prevented before they reach the ICS/OT network. In the case that the threats breached the networks, then they have solutions for that too.
Forescout went all out and acquired ICS/OT Cyber security specialist Security Matters in November last year. While they have managed to integrate the solutions up to a point, a year later there are some gaps that are yet to be addressed.
Another interesting point was that, while the target audience for most vendors is still clearly process manufactures and critical infrastructure, there is a new focus on BMS and medical. Looking at some of Checkpoint’s partners it is indeed not surprising that the medical sector is being seen as a huge opportunity.
Did you visit the conference or have anything to add about the topics discussed? Let us know in the comments section below.
I look forward to catching up with you all at the ICS Cyber Security Conference in Atlanta next month.
Jonathon Gordon
Directing Analyst
Takepoint Research
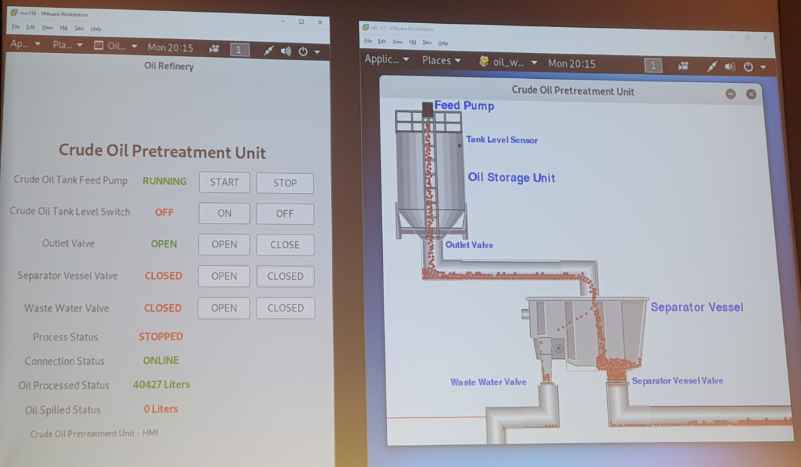
ThinkCyber CEO David Shiffman presented attack scenario
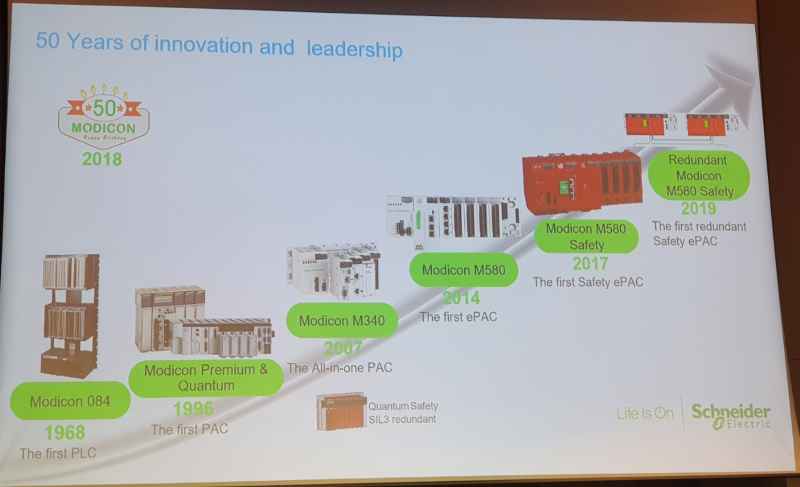
Schneider Electric ‘s Nissim Hai presented a brief history and future of ICS security efforts