Baseline objectives identified by CISA, NIST for cybersecurity performance goals
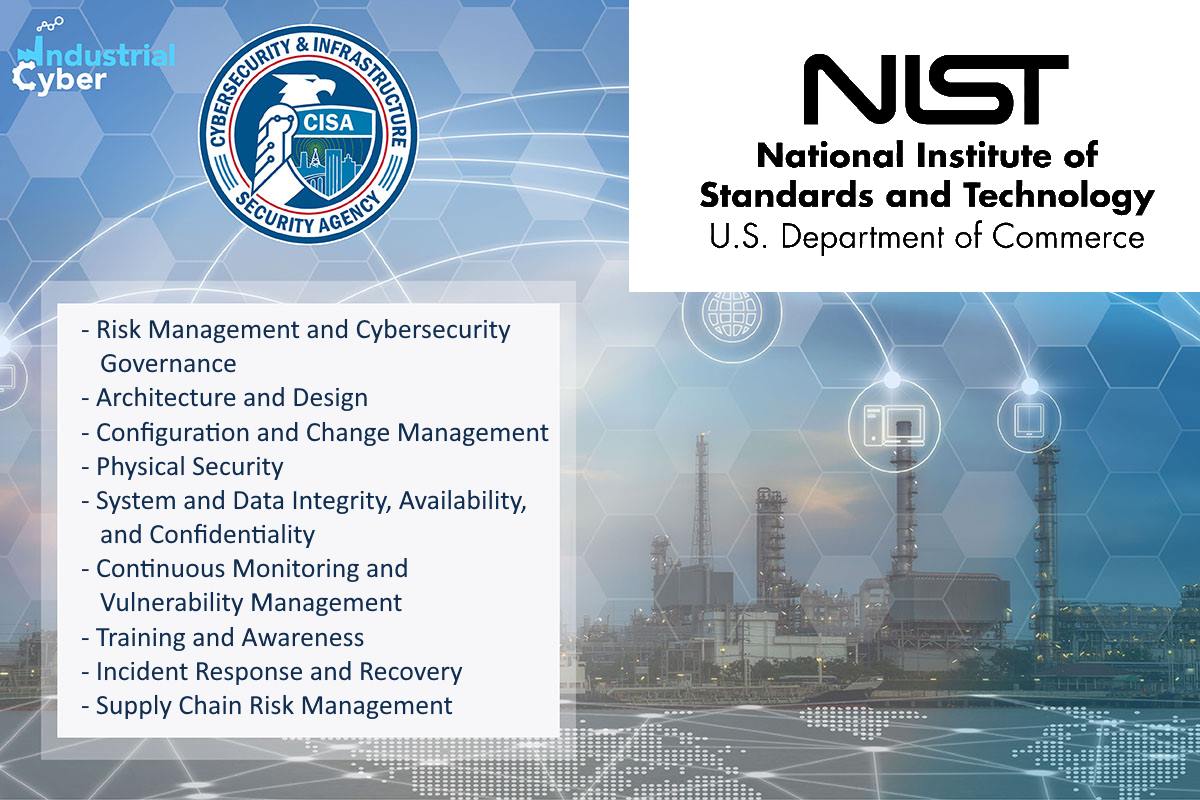
The Cybersecurity and Infrastructure Security Agency (CISA) and the U.S. Department of Commerce’s National Institute of Standards and Technology (NIST) have identified nine categories of recommended cybersecurity practices and used these categories as the foundation for preliminary control system cybersecurity performance goals. Each of the nine goals includes specific objectives that support the deployment and operation of secure control systems that are further organized into baseline and enhanced objectives.
Baseline objectives represent recommended practices for all control system operators while the enhanced objectives include practices for critical infrastructure supporting national defense, critical lifeline sectors such as energy, communications, transportation, and water, or where the failure of control systems could have impacts on safety.
The nine preliminary performance goals and specific objectives include risk management and cybersecurity governance, architecture and design, configuration and change management, physical security, system and data integrity, availability, and confidentiality, continuous monitoring and vulnerability management, training and awareness, incident response and recovery, and supply chain risk management. The order of the goals and objectives is not intended to imply a prioritization or specific progression of operations.
“It is vital that critical infrastructure owners and operators immediately take steps to strengthen their cybersecurity posture toward these high-level goals,” Secretary of Homeland Security Alejandro N. Mayorkas and Secretary of Commerce Gina Raimondo, wrote in a joint statement on the issuance of preliminary cybersecurity performance goals. “The safety and security of the American people relies on the resilience of the companies that provide essential services such as power, water, and transportation. We look forward to further engaging with key industry stakeholders to promote these efforts to protect our national and economic security.”
The Department of Homeland Security (DHS) will coordinate with its interagency and private sector partners to determine the applicability of the enhanced objectives within each sector. In addition to the objectives, an ‘Example Evidence of Implementation’ has been made available for each objective, to demonstrate what successful implementation of an objective might entail for an organization. Successfully implementing all baseline objectives would equate to the successful implementation of a goal.
It is important to note that while all of the goals outlined in this document are foundational activities for effective risk management, they represent high-level cybersecurity best practices. Implementation of the goals and objectives listed here is not an exhaustive guide to all facets of an effective cybersecurity program. These preliminary goals and objectives were developed and refined with as much interagency and industry input as practical for the initial timeline using existing coordinating bodies. DHS expects to conduct much more extensive stakeholder engagement as the goals are finalized in the coming months.
These guidelines come following months of cybersecurity attacks on the nation’s critical infrastructure community, including the SolarWinds supply chain attack, the hack of a Florida water treatment facility, BlackMatter ransomware targeting NEW Cooperative, and another ransomware attack on Colonial Pipeline.
Early August, the administration established a voluntary industrial control systems (ICS) initiative that envisages collaboration between the federal government and the critical infrastructure community to significantly improve the security of the critical systems. The White House has also signed a national security memorandum that will enhance security for critical infrastructure control systems, focused on building cybersecurity and resilience of these systems.
The DHS was instructed to lead the development of preliminary cross-sector control system cybersecurity performance goals as well as sector-specific performance goals within one year of the date of the National Security Memorandum. These goals are intended to provide a common understanding of the baseline security practices that critical infrastructure owners and operators should follow to protect national and economic security, as well as public health and safety.
It was followed by the CISA launching an effort called Joint Cyber Defense Collaborative (JCDC) to lead the development of the nation’s cyber defense plans by working across the public and private sectors to help defend U.S. critical infrastructure. With the initiative, CISA aims to promote coordination across federal agencies, state, local, tribal and territorial (SLTT) partners, and private sector entities to identify, protect against, detect, plan for and respond to malicious cyber activity targeting U.S. critical infrastructure.










