Trend Micro debuts TXOne StellarProtect industrial-grade endpoint protection for ICS devices
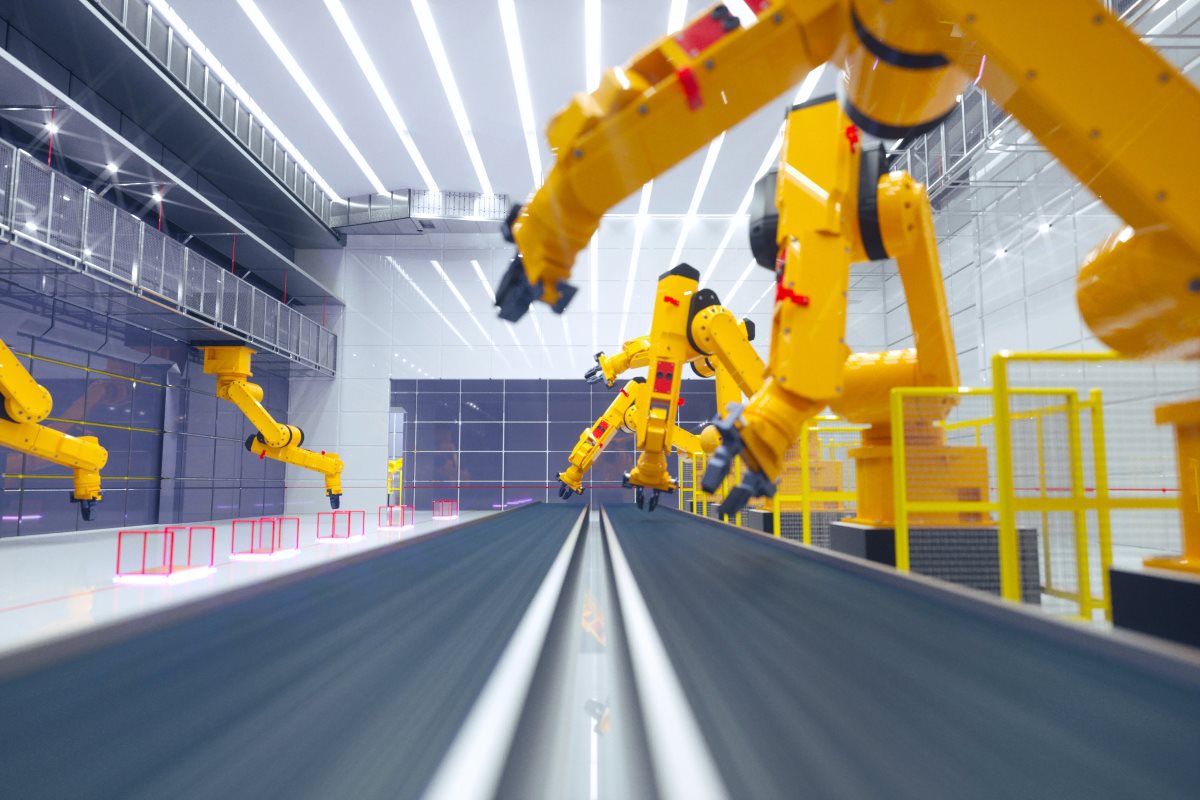
Trend Micro released on Monday its TXOne StellarProtect, an all-terrain endpoint protection defensive solution, custom-engineered for operational technology (OT) environments. ICS endpoints often operate in a harsh environment, where they must provide consistent output and deliver uninterrupted performance.
StellarProtect can operate without an internet connection, using policies designed around “least privilege” to thwart both known and unknown malware, as well as fileless attacks. The OT-native endpoint security solution is provided as part of its total security solution for smart factories and comes developed by TXOne Networks, a company formed by a joint venture of Trend Micro and Moxa. Its advanced threat scanning handles known attacks, while its machine learning engine blocks unknown threats, requiring no internet access.
TXOne StellarProtect provides industrial control systems (ICS)-native endpoint protection against both known and unknown malware via machine learning and ICS root of trust. To avoid redundant security scans and ensure minimal impact to performance, ICS root of trust collects over 1,000 ICS software certificates and licenses and verifies them in advance.
The ICS filtering of TXOne StellarProtect is based on an inventory of applications and certificates. Users will be able to eliminate unnecessary overhead to allow the most lightweight operation possible. Effective in a range of environmental conditions with high accuracy and very low impact on endpoint performance, the TXOne StellarProtect provides full coverage in one deployment.
StellarProtect defends against malware-free attacks due to its least privilege-based policies. Operational interruption from malicious attacks or even misoperation by personnel is prevented by its built-in ICS application behavior learning engine. TXOne StellarOne delivers centralized endpoint security management that integrates MITRE ICS IDs and IOC (indicator of compromise) information for the holistic view of security posture.
The massive number of ICS endpoints in working environments provides a large variety of attack surfaces, as they often include many unpatched or otherwise vulnerable devices. Disruption of these endpoints causes significant problems for manufacturers and can jeopardize the entire operation. The security air gaps, if they ever truly existed, have long gone, as increased connectivity and criticality of these systems has led to greater challenges for their adaptability, resilience, safety, and security.
Securing ICS endpoints introduces difficulties for both operational engineers and security administrators. Though traditional antivirus has long been seen as a core part of defensive strategy, the test of time has shown it brings shortcomings to work sites. All antivirus software requires constant virus signature updates over the internet to be able to identify threats with scans.
This, in turn, places a heavy demand on both CPU loading and memory consumption as intensive I/O hooking is conducted while files are inspected, thereby putting availability at risk even in worksites running modernized operational devices. Safeguarding ICS endpoints requires a different spectrum of consideration – chosen solutions must ensure daily working processes are never jeopardized, computation is never slowed, and production decisions are never delayed.
“The ugly truth of ICS endpoint security is that there has not been any security solution specifically designed for the high-availability needs of modernized equipment in the OT environment,” said Akihiko Omikawa, executive vice president of IoT security for Trend Micro and chairman of TXOne Networks in a company statement. “Cybersecurity solutions for ICS endpoints must consider three elements to meet industry expectations: low impact to performance, zero interruption, and all-terrain protection.”
As manufacturing and smart factories around the world are implementing digital transformation to survive and continue to grow, cybersecurity threats have become a top concern, Trend Micro has pointed out. It released in March details from a recently concluded survey that analyzed the current state and challenges facing industrial cybersecurity, especially in securing manufacturing and smart factories. It looks into the importance of industrial cybersecurity within these environments.










