Industrial cyber security training comes into focus in advancing threat landscape – Part II
Increased focus and demand for OT cybersecurity are driving the need for continued and even greater cyber security training and talent. ICS engineers and system operators must be periodically taught to identify vulnerabilities in ICS environments, determine how attackers can maliciously interrupt and control processes and how to build defenses, and implement proactive measures to prevent, detect, slow down, or stop attacks.
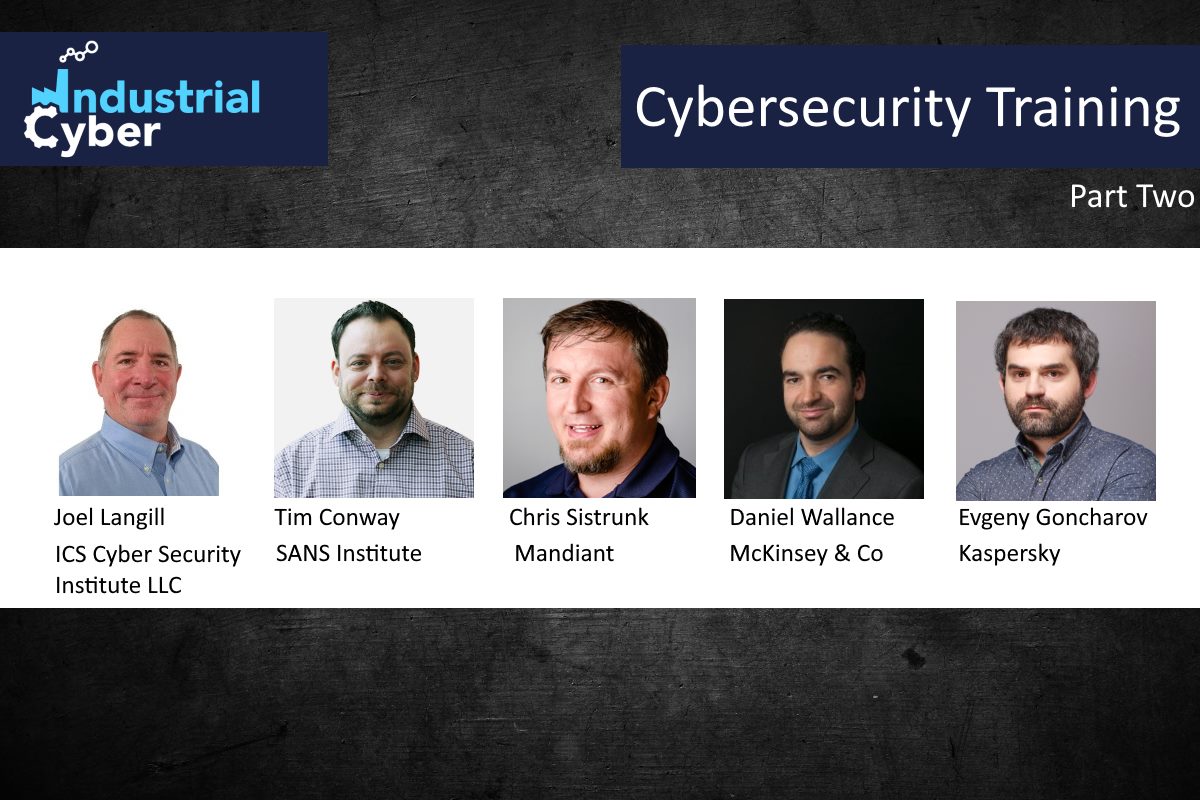
In the second part of our series on industrial cyber security training and certifications, executives discuss with Industrial Cyber whether the lack of training was a reason or contributing factor for the recent cybersecurity incidents. They also talk about the changes that industrial cyber security training and certification have had to make with the increased deployment of digital transformation into the OT environment, and if OT engineers are able to assess and detect if the OT environment is safe, or are organizations having to send them for training and additional certification.
Catch up with the first part of the series here.

Joel Langill Founder & Managing Member – Industrial Control System Cyber Security Institute LLC
Joel Langill does not believe that the lack of training was a contributing factor to the recent cybersecurity incidents such as the SolarWinds supply chain attack and other recent attacks. “The root cause is the failure to have an established industrial cyber security program in place that is tailored to each particular company and their specific operational requirements,” Langill, founder and managing member at Industrial Control System Cyber Security Institute (ICSCSI) told Industrial Cyber.
“All of this is based on a rigorous risk management program, that if in place, would have realized the potential threat entry points that solutions like Solarwinds offered, and should have been appropriately secured. I believe the real root cause in these and likely more attacks in the future is from the failure to properly identify and quantify operational risk and apply security controls and countermeasures to mitigate this risk. Operational security is different from information security and must be addressed as such,” Langill added.
“While I am not aware of the depth or scope of the IT / OT cybersecurity training programs at the organizations that were recently victims of operations impacting attacks, there are certainly benefits to be had from cybersecurity training programs that focus on the unique training needs of learners based on their individual specific roles and responsibilities,” Tim Conway, technical director – ICS and SCADA programs at SANS Institute. “It is important to implement programs that address security awareness across an organization’s users and IT and OT cybersecurity training to help mitigate potential impacts of operational systems. This will improve an organization’s detection, prevention, and response capabilities.”

Tim Conway, technical director – ICS and SCADA programs at SANS Institute
Recent cybersecurity incidents across the industrial sector further emphasize the need for OT cyber security training and talent. “In response to these attacks the demand for OT cybersecurity talent has only increased by companies seeking to improve their cybersecurity capabilities with a focus on OT cybersecurity but also for IT-dependent systems,” said Daniel Wallance, associate partner at McKinsey & Company. “Training and talent development is essential to meet these needs and the overall growing demand. However, training is not limited just to OT cybersecurity practitioners, rather all employees need security awareness training as the ‘first line of defense,’” he added.
Continued cyber security training and awareness are important to influence and drive good organizational cybersecurity behavior, according to Wallance. “At the same time there is no silver bullet for addressing all cyber-attacks but focusing on a comprehensive approach across technology, processes and people including training will limit the impact of cyber-attacks,” he added.
Chris Sistrunk, technical manager at Mandiant ICS Consulting said that for the SolarWinds supply chain attack, the lack of training was not a reason or contributing factor. “It was a targeted attack by a seemingly determined and well-funded criminal attacker group. Targeted supply chain attacks are hard to prevent…however it’s possible to limit damage and recover quickly by how well trained the incident response team was to act,” he added.
However, “For Oldsmar, I would say yes. This event could have been prevented with proper Security Awareness Training and analysis of their systems to make sure they were not connecting their ICS/OT to the Internet,” Sistrunk added.
Evgeny Goncharov, head of Industrial Control Systems Cyber Emergency Response Team (ICS CERT) at Kaspersky also distinguished between the SolarWinds attack and the Oldmsar water plant hack.
“The Oldsmar water plant attack was a low-sophisticated attack. Though the attacker easily made it to the plant’s OT systems, the OT personnel managed to detect the intrusion and to roll the malicious modifications back, preventing the damage,” Goncharov said. “That’s an example of how a safety measure could be helpful protecting against an unsophisticated threat. This wouldn’t be enough in case of a more skilled and motivate malicious actor and by no means the incident say that the OT personal does not require intensive cybersecurity trainings,” he added.
“On the other hand, the SolarWinds supply chain attack showcases the OT is highly dependent on IT nowadays. Even for a well-trained professional, it is hard to protect from a 0-day vulnerability exploit,” Goncharov pointed out.
Recognizing that changes to industrial cyber security training and certification have had to be made with the increased deployment of digital technologies into the OT environment, Conway said that, “We are in a continuous update cycle for the training content and hands on labs contained within our ICS focused cybersecurity curriculums. We are always working hard to identify and develop additional courses that are of greatest need.”
“I believe that certification programs are not a valuable attribute to obtaining a safe, secure and resilient industrial control environment,” Langill said. “They are based on a basis of knowledge and not on learning, reinforcing and deploying operational skills necessary to identify and correct operational risk and improve overall resiliency of the cyber-physical systems,” he added.
Sistrunk said that the “OT cybersecurity training and certification has grown over the years from a few compliance-based trainings and the free courses from DHS/ICS-CERT/CISA, to many companies, including Mandiant.”

Daniel Wallance, associate partner at McKinsey & Company
McKinsey’s Wallance said that when conducting digital transformations cybersecurity including OT cybersecurity should be built in from the start to protect the investments made.
“Digital transformations can have significant business impact but need to be properly secured in order to protect the value created. Therefore this results in the need for greater cybersecurity and OT cybersecurity talent either internally developed or externally sourced,” according to Wallance. “Similarly the OT cybersecurity talent also needs to be well versed in digital and business drives for digital transformations to be able to further unlock the business value through good cybersecurity,” he added.
“The digital transformation, as I see it right now, requires some major priority and approaches changes for both the industrial object owners, the technology/service providers, and the product vendors,” Goncharov said. “By now, almost all the OT products and infrastructures are built with regard to the “safety by design” concept, while the security measures and controls are placed on top of the existing technology and architecture, rather than being an essential integral part of it,” he added.
“To fully accept the digital transformation ideas and make use of them without dramatically sacrificing both security and safety, all the products and infrastructures should also incorporate the ‘security by design’ concept,” according to Goncharov.

Evgeny Goncharov, head of Industrial Control Systems Cyber Emergency Response Team (ICS CERT) at Kaspersky
“This would require new cybersecurity certification and acceptance for technologies, products and infrastructures, such as concepts like the IoT Security Maturity Model by IIC,” Goncharov said. “That does not mean the current security awareness and training approaches and schemes for personnel (such as the ones mentioned above) are not applicable, they just need to be upgraded to incorporate the new concepts and technology changes,” he added.
Talking on whether OT engineers were able to assess and detect if the OT environment is safe, or are organizations having to send them for training additional certification, Conway said that “within OT environments, gaining visibility across the dynamic assets and endpoints can be very challenging and understanding what is being seen and developing a detection capability can be even more challenging.
“Therefore, leveraging the information in a manner that informs a response can be challenging without assistance,” according to Conway. “In the ICS515 course from SANS Institute and the associated GRID certification, there is a specific ICS focus on achieving OT visibility, detection, and response capabilities that support operations objectives,” he added.
“Events like Solarwinds will continue as long as IT drives cyber security architectures without a true understanding of operational risk,” Langill said. “I have been on numerous assessments where IT ‘security’ solutions are deployed that violate basic operational security philosophies and provide ‘convenience’ rather than ‘security. OT and IT will always be different … because OT is responsible for its final actions to manipulate physical systems.”
As such, the driving factor must always be how any deployment could impact essential business functions in terms of health, safety, and environmental responsibility, Langill added.
“Organizations need to have effective cybersecurity capabilities including patch/vulnerability management, anti-malware capabilities, and network segmentation that cover the OT environment, Wallace said. “However, to ensure the effectiveness and coverage of these controls requires advanced technical testing and validation. The objective is to validate both the effectiveness and coverage of the full set of OT cybersecurity controls that exist at an industrial organization.”
“There’s no such a knowledge or experience that is enough forever. I neither actually think the SolarWinds case has dramatically changed things for both IT and OT security,” Goncharov said. “It’s neither the first nor the last case of a wide-scale attack affecting multiple organizations, so absolutely, the training for the personnel is still required and will be always required until the things are fully automatic and no humans are needed to control or maintain them.”

Chris Sistrunk, technical manager at Mandiant ICS Consulting
“Even at this stage, the hard skill training for the cybersecurity professionals would still be required, as I believe the cybersecurity would need the professionals for quite a while in the future,” Goncharov added.
“OT Engineers were not trained on OT Security in College courses…until the last 2-3 years. However, due to the increasing amount of OT Security practitioners, increasing OT security regulations, and increasing free training opportunities…OT engineers are better to assess these incidents,” Sistrunk said. “However we still have a long way to go, because to be honest, OT Security Incidents are few compared to IT Security Incidents.”
Sistrunk said that OT engineers should be able to protect and respond against an Oldsmar type of incident rather easily. “OT engineers are not equipped to respond to detect to novel (never before seen) Supply Chain Attacks on their own…they need additional resources like SOC analysts and IT incident responders and possible malware reverse engineers to handle targeted attacks,” he concluded.










