Rise in IT/OT convergence drives increased automotive cybersecurity
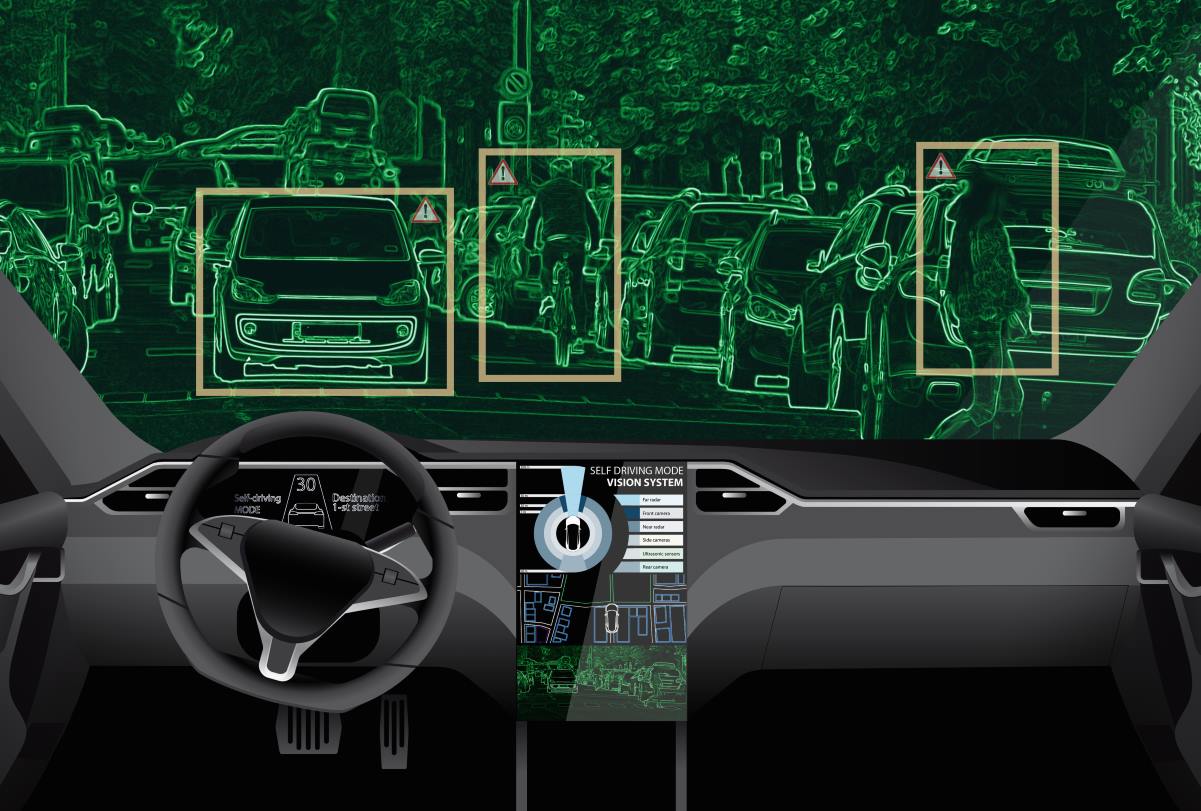
With the increased proliferation of smart devices and sensors in the automotive industry, connected vehicles are becoming more prone to cyberattacks. To better deal with the new challenges, an increased need for a comprehensive risk-based approach to automotive cybersecurity allows for the seamless management of cybersecurity risks throughout the vehicle lifecycle, while also providing visibility and insight to optimal mitigations, according to a blog post.
The digitalization of crucial vehicle components and growing adoption of IT/OT convergence in the automotive industry introduces many new challenges, in addition to bringing about various benefits, wrote Saif Shariff and Anastasios Arampatzis in an Orignix blog post. Orignix works with various stakeholders in the critical infrastructure sector, and helps in managing interdependencies between industrial automation and control, safety, security, and IT systems to bring about increased cybersecurity, industrial automation and process safety.
The comprehensive risk management process will allow car manufacturers to know their major risks, understand the size of their attack surface, assess the criticality of their digital infrastructure based on the vehicle types, and inventory connected systems, and then use this intelligence to add resilience in a targeted and prioritized manner, the blog post added.
Managing and having oversight of cyber risks is one of the critical challenges, according to Orignix. The increased threat landscape raises the profile of automotive cybersecurity as a strategic risk. This significant risk must be mitigated, and automotive cybersecurity should not be focused solely on traditional IT security controls. The extensive and complex supply chain involved in car manufacturing requires a disciplined approach to examining and addressing the cyber-physical risks, it added.
Security gaps and vulnerabilities may also occur when modern, connected devices are layered on top of legacy automotive networks like the CAN bus, according to the post. These connected devices can inadvertently expose sensitive systems to open networks and leave them vulnerable to malicious exploits.
At many automotive OEMs, cybersecurity has become a top concern, McKinsey identified in its ‘From no mobility to future mobility: Where COVID-19 has accelerated change’ report released in December 2020. Currently, only narrow standards and guidelines exist for specific technical procedures for securing hardware and software in vehicles, such as standards for hardware encryption or secure communication among ECUs. That will soon change, however, it added.
“The World Forum for Harmonization of Vehicle Regulations (WP.29), under the UN Economic Commission for Europe, is planning to release new regulations on cybersecurity and over-the-air software updates,” according to McKinsey. The cybersecurity market is expected to have a compound annual growth rate of 7 percent through 2030, when it will reach US$9.7 billion in value, it added.
Automakers and the automotive industry seem to be getting special attention from ransomware threat actors. One of the possible reasons identified by industrial cybersecurity firm OTORIO is that attackers have identified the automotive segment as more vulnerable than others, and they are exploiting it.
Last month, Kia Motors America (KMA) confirmed that it was experiencing an extended systems outage. The company, however, said at the time that it has seen no evidence of having suffered a ransomware attack, but apologized to customers for the outage, which the car maker affirmed it was working to resolve at the earliest with minimal disruption to the business.
Nozomi identifies IT/OT convergence across all subsectors of the transportation industry as making perfect sense because operational technology (OT) data, once completely segregated from everything, can be merged with IT data, and shared throughout the organization to provide richer insights and help in decision making. Unfortunately, most OT security teams lack the tools, skills, or resources needed to manage IT/OT cross-pollinated environments, according to a Nozomi blog post.
The digitalization is forcing OT security teams to shore up their side of the fence, beginning with evaluating their systems and networks, understanding the potential security gaps, and agreeing on what it means to be cyber-ready, according to Nozomi. It helps to put aside the mindset around legacy applications that have been running these systems for decades.
“Security teams need to embrace digital systems that provide enormous operational benefits… along with an increased level of potential security holes and incidents,” Nozomi added.










