Kaspersky report reveals barriers in industrial cybersecurity project implementation

Cybersecurity company Kaspersky has released a new report looking at the state of industrial cybersecurity in the era of digitalization along with the current priorities and challenges facing industrial organizations. The report reveals barriers standing in the way of industrial cybersecurity project implementation.
“The cybersecurity race doesn’t slow down, and every year many incidents, including high-profile attacks, are hitting industrial control systems (ICS),” Kaspersky said in a press release. The pandemic lockdown introduced its own challenges in addition to the existing threat landscape. Industrial firms have to adapt to new norms including remote work, overnight digitalization and new hygiene requirements, as well as specific pandemic-driven threats such as a massive growth in phishing attacks. Organizations need to make sure their protection is up to date with these changes and there are no open doors for malicious actions in ICS networks.”
The report includes the results of a 2020 survey conducted by ARC Advisory Group, a technology research and advisory firm for industry and infrastructure. ARC surveyed more than 330 industrial companies and organizations, and conducted interviews with 10 industry representatives at trade fairs and ARC forums. Respondents came from a range of regions including Europe, North America, Latin America, Asia, and the Middle East.[optin-monster-shortcode id=”dv4jqlr9fih8giagcylw”]
“This year was a special survey year. With the coronavirus pandemic and the subsequent industry lockdowns, industrial cybersecurity methods were exposed to new challenges,” the report says. “With the help of the survey results, we have worked out the impact the pandemic has had on existing cybersecurity methods.”
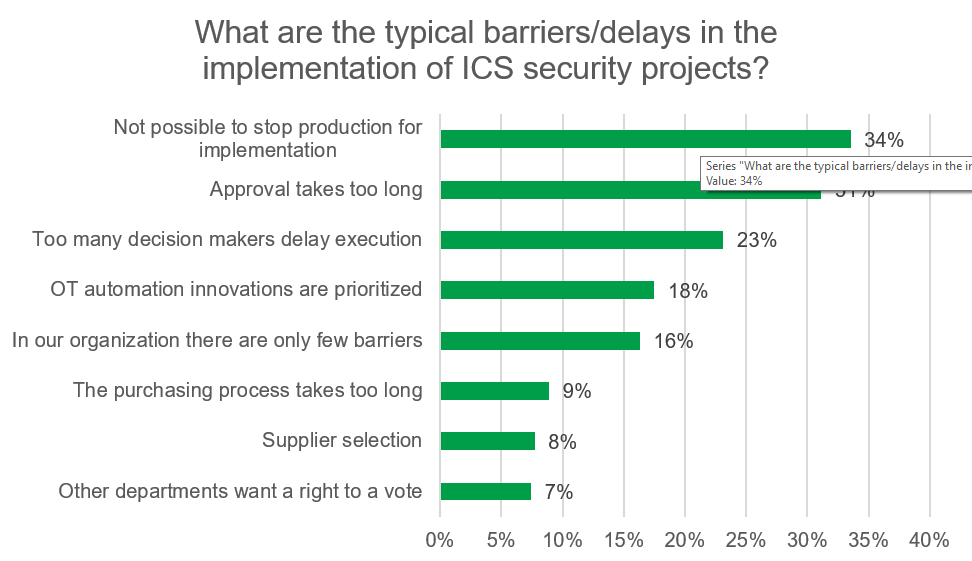
According to the report, red tape is the main barrier to cybersecurity initiatives in the industrial sector. This includes long approval times, numerous decision-makers, protracted supplier selection and purchasing processes, as well as interference from other departments.
Thirty-four percent of respondents identified the inability to stop production as a major obstacle to industrial cybersecurity project implementation. Other barriers identified included bureaucratic steps, such as a lengthy approval process (31%) and having too many decision-makers (23%).
“It’s always more difficult to invest money and resources in projects without a clear return on investment, such as with cybersecurity initiatives,” Georgy Shebuldaev, Head of Growth Center at Kaspersky, said in the press release. “And while cybersecurity for OT is still a developing area, all these management barriers are quite natural. As a vendor, it is up to us to help customers eliminate these obstacles and simplify and speed up the implementation of protection measures. Our task here is to make ROI more transparent and showcase the risks for businesses so customers can understand the benefits from the very beginning and better justify them to C-suite or the board if needed.”
The report also looked at how the COVID-19 pandemic has impacted cybersecurity at industrial organizations. Forty-six percent of respondents said they expect to see changes in their OT security priorities as a result of the pandemic. Whether or not these changes will accelerate industrial cybersecurity project implementation is unclear.
“These organizations will probably need to shift their security strategy on-the-fly and quickly implement new cybersecurity practices,” Kaspersky said in the release. “While it can be challenging generally, due to the specific requirements of OT, the barriers for implementation can complicate and slow down the process even more. Some organizations will need to be even more conscious as they try to overcome these difficulties with decreased OT security budgets.”
Fifty-three percent of respondents said they have been operating with a remote workforce. And as a result, 14 percent of organizations reported revising their cybersecurity concepts. Only seven percent said their cybersecurity strategy was sufficient during the pandemic.
“The increase in the number of remote workers drove up the number of OT network scan attempts during the pandemic,” the report says. “The result was that companies recognized the need to supplement cybersecurity procedures during exceptional situations.”
Researchers also examined cybersecurity maturity at the organizations surveyed. Fifty-five percent of respondents said their OT networks are checked for security issues at least once a year or more often. Additionally, 44 percent said they work on cybersecurity initiatives for digital transformation every day.
“Industrial cybersecurity has changed significantly in recent years,” the report says. “Sophisticated attacks have increased the demand for better visibility of the cyber-risks that impact control systems. The integration of IT and OT cybersecurity programs has highlighted the need for increased system access by remote support teams. Digital transformation programs require new approaches to ensure the secure deployment of a variety of new, potentially unsafe devices within plant boundaries.”
Each year Kaspersky’s annual report looks at the top cybersecurity challenges organizations are facing. Thirty-two percent of respondents said deaths and accidents caused by hazardous substances are the biggest threats facing industrial organizations. Respondents also cited damage of service quality, loss of confidential information, and mitigation costs as major challenges.
“This year, the effects after an attack and the resulting costs were especially important,” the report says. “In 2019 the situation was different. In that survey, the cost of incident response and loss of customer confidence were deemed to be rather unimportant (only 5%). It’s clear that a new perception is emerging. Due to the increasing sophistication of cyberattacks against industry assets6, the effects are more noticeable. In addition, operational units now regularly report to the board of directors so that the effects after a cyber-incident can be better analyzed.”
In addition to revealing survey findings, the Kaspersky report also makes a series of recommendations for industrial cybersecurity project planning and implementation. Specifically, they recommend anomaly detection as a key practical measure for protecting organizations against ICS threats.
“Anomalies are unexpected deviations from the normal rules, i.e. deviations from ‘normal operating conditions’. These usually occur in the event of an error,” the report says. “However, they can also be an indication of an attack or manipulation within a production network. This is especially true when events occur for the first time, processes behave differently, or devices communicate with each other that have not done so before. It means that previously unknown attack patterns can also be detected by evaluating anomalies. Anomaly detection is therefore a suitable method of generating cyber-warnings and, if necessary, enabling more effective forensics.”
The report also suggests organizations adopt a cybersecurity maturity model like ARC’s. The model provides a framework for strategically developing the benefits of cybersecurity technologies for risk reduction in industrial processes.
“This cybersecurity model for evolving technologies and architectures goes beyond the recommendations of standards and guidelines by incorporating new OT technologies, such as edge gateways, new practices such as PKI and new strategies, including the integration of IT and OT cybersecurity programs,” the report says. “Efficiency gains are driving companies to adopt these developments despite a lack of industry guidelines. We have incorporated these developments into the model to help cybersecurity teams better assess and prepare for these developments. ARC’s cybersecurity analysts regularly update this industrial OT cybersecurity maturity model. We have incorporated new technologies and practices used within industrial cybersecurity. In summary, this ARC model provides a practical tool for planning cybersecurity investments.”










