Memory protection bypass vulnerability allows remote access to Siemens PLCs
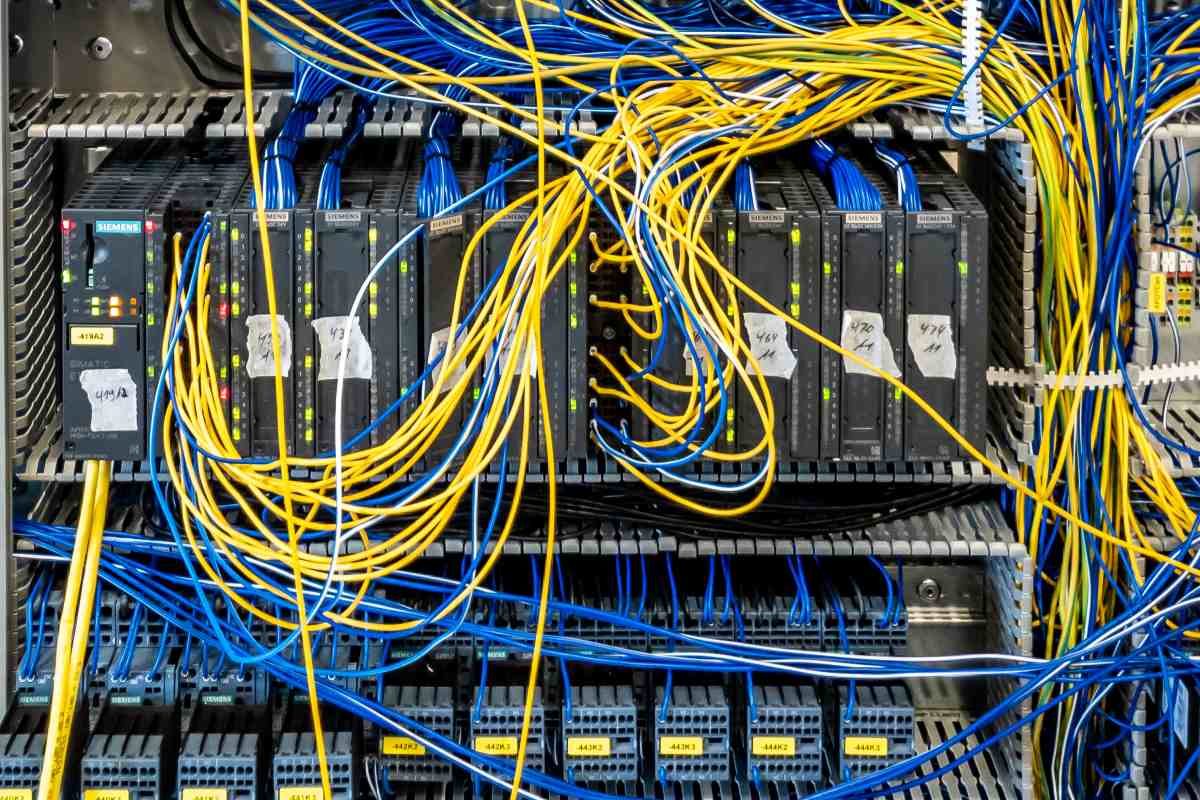
Claroty has detected a memory protection bypass vulnerability in two Siemens’ SIMATIC PLCs (programmable logic controllers), which could be exploited by an attacker with disabled access protection. The loophole could let the remote unauthenticated attacker with network access to TCP port 102 to potentially write arbitrary data and code to protected memory areas or read sensitive data that would be difficult to detect and remove, in addition to launching further attacks.
Claroty is not aware of any public exploitation of this vulnerability. The firmware of both the SIMATIC S7-1200 and S7-1500 PLCs has been updated by Siemens. Users are urged to update to the latest versions.
The German conglomerate said it is preparing further updates not currently available for the affected products, and provided specific mitigation measures for users to reduce risk. Siemens acknowledged the role of Claroty researcher Tal Keren for his coordinated disclosure.
PLCs have numerous in-memory protections that would have to be overcome in order for an attacker to not only run code of their choice but also remain undetected.
The bypass vulnerability avoids existing protections within the execution environment of the PLC, including a sandbox where engineering code would normally run. Claroty was able to use this vulnerability to escape the sandbox, in order to gain direct access to memory, then write and inject shellcode to execute an attack on Siemens 1200/1500 PLCs.
“The integrity of a PLC is crucial to operators and engineers, and an attacker’s goal would be to damage that integrity by hiding code on the controller and elevating privileges,” Keren wrote in a Claroty executive summary.
“This disclosure is an outcome of Siemens’ and Claroty’s existing partnership, which fosters not only tight cooperation between our research team and the vendor on disclosures but also in the security of the overall industrial ecosystem,” according to the summary. “The close coordination between Siemens and Claroty included an exchange of technical details, attack techniques, and mitigation advice that helped shape the patches available in today’s update from Siemens.”
In order to execute an attack, one would need network access to the PLC. In addition, the attacker would need PLC download rights. Since TIA Portal (Totally Integrated Automation Portal) V12, Siemens provides various mitigation controls to limit user network and read/write access to the PLC, especially the password protection mechanism, Keren said.
Additionally, starting with V17, Siemens introduces TLS (transport layer security) communication using individual certificates between PLCs, HMIs (human-machine interface) and TIA Portal, which reduces the potential attack surface.
To understand the specific attack using the generic structure of a standard PLC, its CPU is either a 16- or 32-bit microprocessor consisting of a memory chip and integrated circuits that manage control logic, process monitoring, and communication. The CPU directs the PLC to execute control instructions, communicate with other devices, carry out logic and arithmetic operations, and perform internal diagnostics.
It also runs memory routines, constantly checking the PLC to avoid programming errors, and ensure the memory is undamaged. The logic runs in a sandbox environment, which may sometimes be referred to as ‘jail,’ according to Keren.
The logic being transferred to the controller is limited to specific memory regions and APIs provided by the vendor. In the case of the Siemens S7 PLCs, which runs on the ADONIS kernel and an ARM or MIPS processor, there are numerous programming languages available to configure the controller, including Statement List (STL), Ladder Diagram (LD), Function Block Diagram (FBD), and Structured Control Language (SCL).
Regardless of input sources, the PLC program will be compiled into MC7 / MC7+ bytecode, which is a lower-level representation of the code, according to the summary. After being compiled by the Siemens TIA Portal, the code blocks (in MC7/MC7+ format) are downloaded and installed into a PLC via Siemens’ S7Comm / S7Comm+ protocol. Then, the MC7 virtual machine in the PLC will dispatch the code blocks and interpret and execute the bytecode.
It is not possible to decode MC7/MC7+ bytecode without reverse engineering, because Siemens has not publicly provided documentation to do so. Therefore, Keren had to reverse engineer the MC7/MC7+ bytecode language set in order to understand its internal mechanism and find bugs, the summary said.
Since the virtual machine restricts the resources accessed by the users’ programs, the compiled bytecode can only be used for access to the allowed resources by the operating system rather than direct hardware operation, in order to restrict the user and the running code to a defined set of actions that are considered safe. Thereby, leading the operating system to ‘locking’ the user’s code in a sandbox/container with limited access to resources, memory, and functionality that could potentially damage the PLC and/or the entire process.
In order to escape, or ‘jailbreak,’ the native SIMATIC S7-1200 and S7-1500 sandboxes, Claroty used its memory protection bypass vulnerability, which enables an attacker to write arbitrary data and code to supposedly protected memory areas, or read sensitive data to launch further attacks, according to the summary. Escaping the sandbox means an attacker would be able to read and write from anywhere on the PLC and could patch an existing VM opcode in memory with malicious code to root the device.
Claroty, for example, was able to inject ARM/MIPS shellcode directly to an internal operating system structure in such a way that when the operating system uses a specific opcode that we chose, our malicious shellcode would execute, giving us remote code execution. “We used this technique to install a kernel-level program with some functionality that is completely hidden to the operating system,” Keren added.
Siemens and Claroty advised users to apply the S7-1200 and S7-1500 CPU updates and protect from the bypass vulnerability, in addition to the updates for other affected products given the critical nature of this vulnerability, the advisory added.










