GAO says agencies must fully adopt NIST framework for critical infrastructure protection
Recently the United States Government Accountability Office released a new report on critical infrastructure protection.
According to the report, 12 of the organizations tasked with protecting the nation’s critical infrastructure are voluntarily using the National Institute of Standards and Technology’s Framework for Improving Critical Infrastructure Cybersecurity. However, some of the organizations are only partially using the framework and not all of them are collecting or reporting on improvements from using the framework.
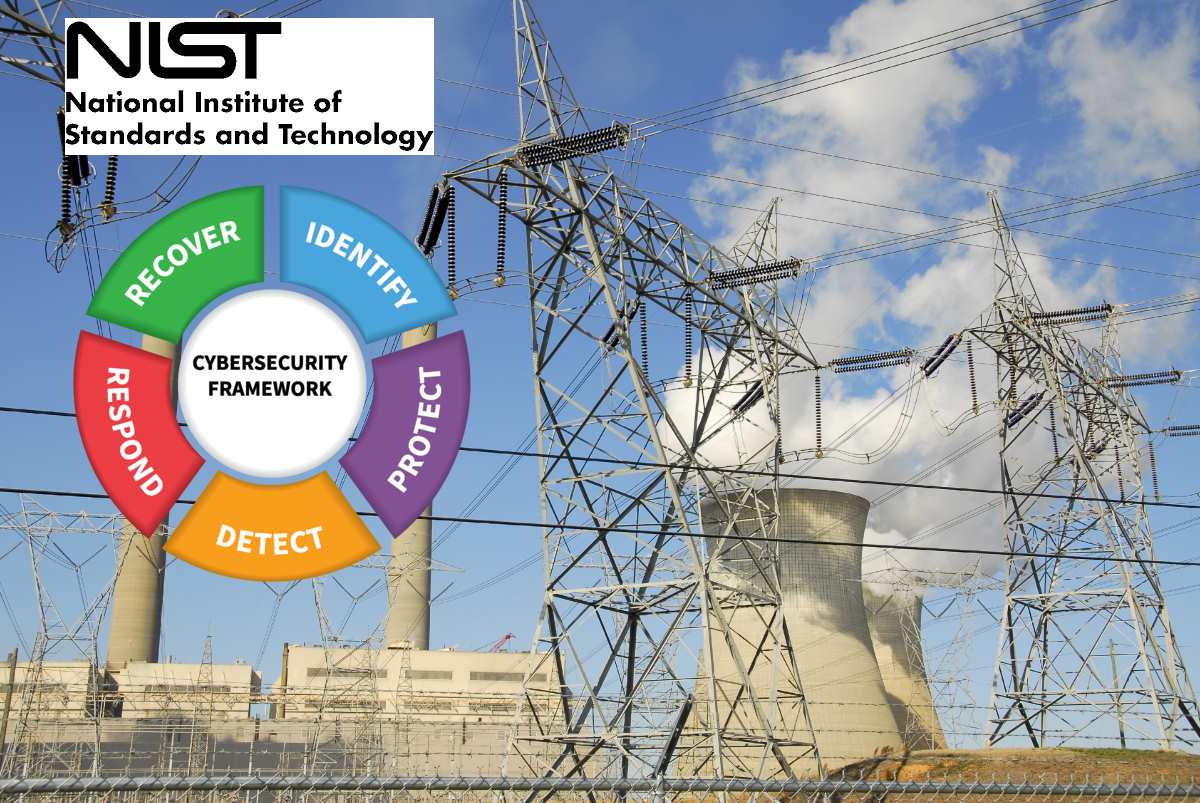
“Cyber threats to the nation’s critical infrastructure (e.g., financial services and energy sectors) continue to increase and represent a significant national security challenge,” GAO says in the report. “To better address such threats, NIST developed, as called for by federal law, a voluntary framework of cybersecurity standards and procedures.” [optin-monster-shortcode id=”dv4jqlr9fih8giagcylw”]
The NIST framework is designed to help an organization better understand, manage, and reduce its cybersecurity risks specifically with regards to critical infrastructure protection. It covers utilities, transportation, financial services, communications, healthcare and public health, food and agriculture, chemical and other facilities, dams, key manufacturers, emergency services and more.
“The nation’s critical infrastructure provides the essential services—such as banking, water, and electricity— that underpin American society. The infrastructure relies on electronic systems and data to support its missions,” the report says. “However, cyber threats to the critical infrastructure continue to increase and represent a significant national security challenge. In this regard, malicious actors have intruded and extracted highly sensitive materials from the networks of a number of government agencies and major critical infrastructure companies.”
As part of it’s analysis, GAO selected six critical infrastructure sectors identified in the 2018 National Cyber Strategy of the United States of America as having critical infrastructure with the greatest risk of being compromised. GAO then randomly selected one large and one small or medium organization from each sector.
GAO then conducted interviews with these 12 organizations in an effort to understand the level of framework use and related improvements and challenges. The organizations reported varying levels of resulting improvements, including the ability to identify risks and implement common standards and guidelines.
However, the organizations have not collected and reported sector-wide improvements. Their reasons for failing to do so include the lack of precise measurements of improvement, lack of a centralized information sharing mechanism, and voluntary nature of the framework.
To address these impediments, GAO has highlighted initiatives created by NIST and the Department of Homeland Security. For example, DHS’ homeland security information network was designed to be the primary system for reporting on best practices, including sector-wide improvements and lessons learned from using the framework. Additionally, NIST’s Roadmap for Improving Critical Infrastructure Cybersecurity , version 1.1, includes a tool that helps organizations self-assess how effectively they manage cybersecurity risks and identify improvement opportunities.
“Although NIST and DHS have identified initiatives to help address the impediments, the [sector-specific agencies] have not reported on sector-wide improvements,” the report says. “Until they do so, the extent to which the 16 critical infrastructure sectors are better protecting their critical infrastructures from threats will be largely unknown.”
As part of the report, GAO recommends the Department of Agriculture, Department of Defense, Department of Energy, Environmental Protection Agency, General Services Administration, Department of Health and Human Services, DHS, Department of Transportation, and Department of the Treasury take steps to consult with respective sector partners to collect and report sector-wide improvements from use of the framework across their critical infrastructure sectors using existing initiatives.
“Most of the SSAs have not determined the level and type of framework adoption, as we previously recommended,” the report concluded. “Most of the sectors, however, had efforts underway to encourage and facilitate use of the framework. Even with this progress, implementation of our recommendations is essential to the success of protection efforts.”










